Introduction: Microsoft Intune is the one of the component of Microsoft Enterprise Mobility +Security. Microsoft Intune is basically allowing organisation for managing the mobile and remote devices, mobile based applications, and prevent data leakage from various corporate applications used by users on their devices.
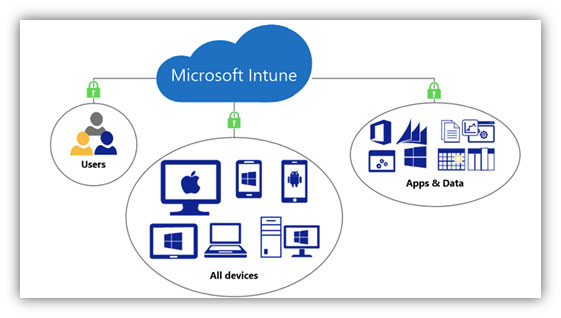
Fig: Microsoft Intune (Image credit Microsoft)
By using Intune as a solution, below tasks can be achieved:
- Manage Android and iOS devices.
- Manage Windows 10 devices.
- Manage mobile based applications.
- Manage data available on applications well as on the devices.
- Data based restriction compliance policy so that data leakage can prevent.
Licensing: In order to use Intune as a service, customer need below licenses is required:
- Enterprise Mobility + Security E3
- Enterprise Mobility + Security E5
- Intune
- Microsoft 365 E3
- Microsoft 365 E5
- Microsoft 365 F1
- Microsoft 365 Business
If organisation wants to use only Intune services they can go with Intune standalone license otherwise it is the part of EMS and M365 which is provide few additional functionalities.
Need of Mobility:
Organizations are increasingly connection with contracted teams, business partners, franchisees, and/or dealers with the same apps that full-time employees use. The fact is many employees are using their personal devices in the workplace via BYOD, today’s IT organization is tasked with securing and supporting corporate apps on devices they do not own or do not entirely control. In this new world, it is vital to ensure security and governance of corporate assets —the mobile apps development company and content— used by this distributed enterprise. Now mobility via Intune provides you the controls as well as the access with security for the end user.
Component of Intune:
Functionality wise Intune is classified into two categories:
- Mobile Device Management (MDM)
- Mobile Application Management (MAM)
By using Mobile device management, organisation can apply some sort of controls or policies directly on devices such as mobile lock code, Wi-Fi block, tethering block, camera block, providing Wi-Fi profile, Email profile etc.
By using Mobile application management, organisation can apply control directly on the corporate applications such as Microsoft Outlook, Word, Excel, Power-point or any in-house application.
On uber level MDM will only be apply on device level whereas MAM can be apply on application level.
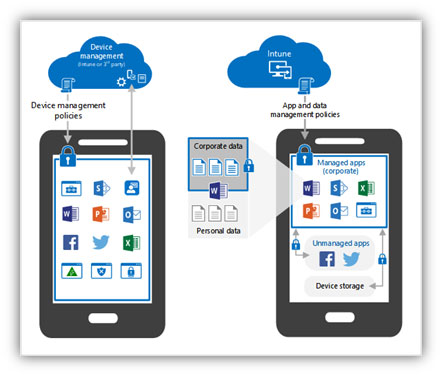
Fig: Corporate data management via MAM.
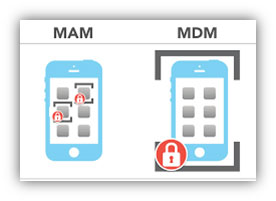
Fig: Difference between MAM and MDM.
Most of the organisation preferred Mobile application management as it will only cover application level of management. Most of the user of an organisation not allowing admin team to perform restricted task on their own phone, hence team is putting restrictions only on the corporate applications.
Functions can perform with Mobile Device Management:
Following action/functionality can be performed in terms of Mobile Device management capability:
- Create/Amend/Edit/Delete Custom Configuration Policy using OMA-URI settings.
- Configuring Compliance and device restriction policies.
- Configuring APN certificate for iOS devices.
- Publishing available and mandatory apps to devices.
- Configuring Application wrapping for Custom Mobile apps.
- Configuring and publishing Wi-Fi profile.
- Configuring and publishing e-mail profile.
Functions can perform with Mobile Application Management:
Following action/functionality can be performed in terms of Mobile application management capability:
- Configuring Mobile application package.
- Configuring Mobile application level policies.
- Application wrapping.
- Application data wipe.
What's New with Microsoft Intune and Configuration Manager: recap the biggest announcements from #MSIgnite https://t.co/Xm3ylI9piD pic.twitter.com/X4UXd6AE5R
— Microsoft Intune (@MSIntune) September 26, 2018
Enterprise Integration and Platform Extensibility:
Given the pace of evolution in the mobile landscape, decision-makers should be thinking about ways to adapt a particular solution to your organization’s unique needs. In an enterprise setting, a powerful and scalable way to do that is by integrating a solution with existing enterprise systems and management tools. IT organizations and business partners will be able to integrate with and extend their own solutions when needed.